Top suggestions for springExplore more searches like springPeople interested in spring also searched for |
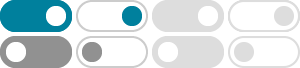
- Image size
- Color
- Type
- Layout
- People
- Date
- License
- Clear filters
- SafeSearch:
- Moderate
- Cyber
Security Learning - Security Learning
Diagram - Cyber Security
Training - Machine Learning
and Security - Security Learning
Environment - Learning
Online Security - Security
Awareness Program - Security Learning
Journey - Self-Learning
Cyber Security - Progress and Learning
in the Security Department - Information Security Learning
Module Design - Security Learning
Library - Learning Security
and Beginners - Security
Training Courses - Office Security Learning
Card - Brigance
Learning Security - Act Security
eLearning - Macine Learning
for Cloud Security - eLearning Cyber
Security - Machine Learning
in Data Security - Security Staff Learning
through eLearning - Learn Cyber
Security - It Cyber
Security - Ai and Machine
Learning in Security - Learning
Confirmation On Information Security - Online Learning
Education - Microsoft Security Learning
Path - Learning Security
Asian Professional - Cyber Security
RoadMap - Vioce Security
by Deep Learning - Security
System Business - Security
Architect - Cyber Security
Presentation - Cyber Security
Certifications - Machine Learning
Course - Cyber Security
Careers - Machine Learning
for Hardware Security - Pacific
Security - Information Security
Skill Update Learning - Security
Consultant - Inspired Learning Security
Wall Papers - Cyber Security
Leaening - Machine Learning Security
Conference Research Poster - Network Security
Projects Using Machine Learning - eLearning Security
Book - Training Learning
Approach in Informatiobn Security - Learning
Table for Security Project - Online Safety
Degrees - Machine Learning Security
Best Books - Azure Machine
Learning Security
Some results have been hidden because they may be inaccessible to you.Show inaccessible results

 Feedback
Feedback